The Vital Importance of Zero Trust Strategies in Today’s Cybersecurity Landscape
Anudeep Parhar serves as the Chief Information Officer at Entrust, a renowned provider of trusted identities, payments, and data protection solutions.
Impactful Cybersecurity Incidents: A Wake-Up Call
In recent months, real-world cybersecurity incidents have underscored their severe consequences. For example, MGM faced an anticipated loss of $100 million following a data breach, while 23andMe allegedly had over one million data profiles sold on the black market.
The Urgent Need for Zero Trust Strategies
The rise of successful phishing and ransomware attacks indicates that cybercriminals show no signs of slowing down. This reality highlights the imperative shift from viewing a robust zero-trust strategy as just a desirable option to an absolute necessity. Despite this realization, many enterprises grapple with the implementation of such strategies.
Challenges in Implementing Zero Trust
A recent survey revealed that enterprises encounter difficulties in full buy-in from various departments to effectively scale zero-trust concepts across the organization. To successfully establish a zero-trust framework, security leaders must secure support from key stakeholders, including the C-suite, and foster collaboration throughout the company. While this process may present obstacles, it remains crucial given the current threat landscape.
Navigating the Zero Trust Paradigm
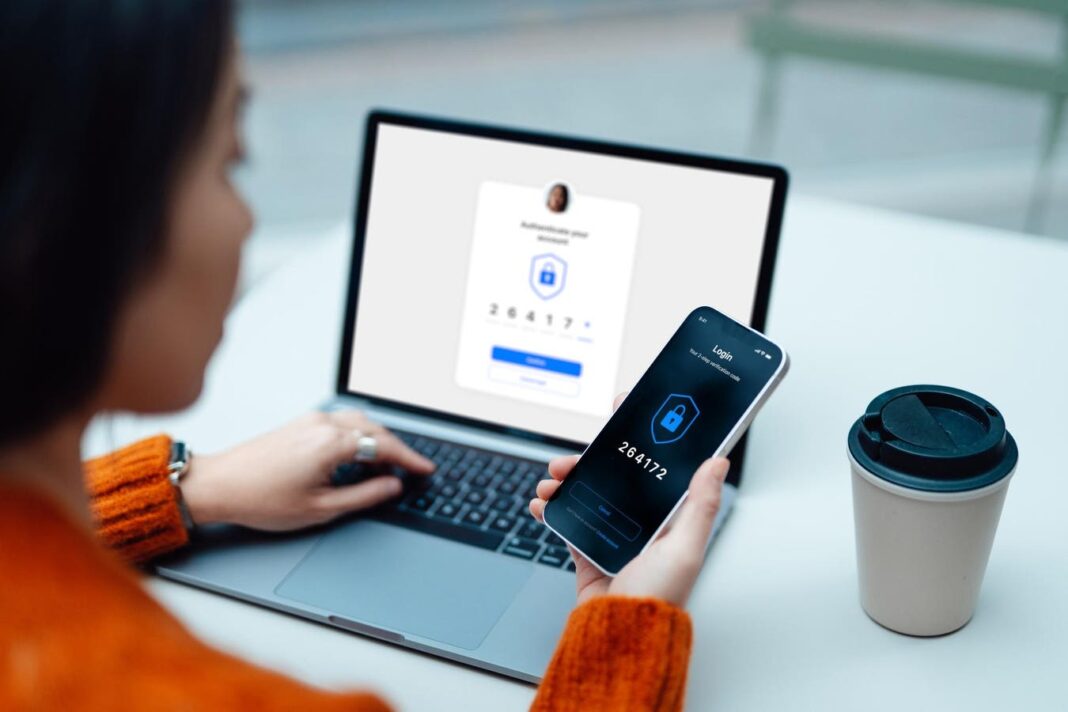
Achieving a zero-trust framework demands a long-term commitment to building trust and collaboration for a solid foundation. This approach involves implementing data encryption with stringent access control policies, ensuring that employees access only necessary data. Traditional security methods have proven inadequate in light of evolving threats, making it essential for organizations to adopt a “never trust, always verify” approach. This strategy involves continuous identity verification and access decisions based on various factors such as role, location, and access history.
Adapting to Evolving Threats
Organizations must assess their current security controls, identify vulnerabilities, and develop strategies to address these gaps. While this process requires significant time and resources, it is vital considering the dynamic nature of modern threats.
Embracing a Proactive Security Stance
Operating under the assumption of an infiltrated system, organizations must focus on preventing unauthorized movements within their network. Security teams should adopt an “always-on” approach, recognizing attackers’ advantage in initiating attacks. Securing buy-in from the C-suite and organizational support is critical in initiating this proactive security stance.
In conclusion, embracing zero-trust strategies is essential in mitigating cybersecurity risks and protecting sensitive data in today’s ever-evolving threat landscape.